What’s the Difference Between Traditional and Hosted VPNs?
Download this article as a .PDF
Connecting programmable logic controllers (PLCs), human machine interfaces (HMIs), and other automation system components to the Industrial Internet of Things (IIoT) for remote access is important for many manufacturing plants, and to the machine builders providing equipment and services to these plants. In the past, remote access was often accomplished via a router without a virtual private network (VPN), but these router-only connections to the internet should not be implemented today due to security risks.
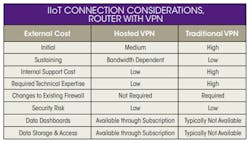
Instead, a VPN should be used, as it is one of the key elements to a defense-in-depth strategy. However, implementing a secure IIoT connection to automation system components via a VPN often presents cost, technical, and resource allocation issues. The two solutions presented in this article address these challenges, but in different ways. Each solution has its own advantages and design considerations, as noted in the table. The two options are hosted VPN and traditional VPN.
The choice to use a hosted VPN versus a traditional VPN depends on three main factors:
- Will all of the IIoT connection needs fall under similar IT conditions, and will each site be able to use the same router configurations?
- Is IT expertise available to support a traditional VPN solution?
- Is high bandwidth required for this solution?
If the answer to any of these three questions is “no,” then the best option is likely the hosted VPN solution. If all three questions are answered “yes,” then the preferred option is likely the traditional VPN solution.
Hosted VPN Solution
A hosted VPN solution provides secure IIoT connectivity with simple setup and network configuration. These solutions usually include a local VPN router, a cloud-hosted VPN server, and a remote VPN client. Automation system components are connected locally to the VPN router, which connects to the cloud server. The VPN client connects by laptop or PC to the cloud, and ultimately to the local automation system components (Fig. 1).
1. AutomationDirect’s StrideLinx secure hosted VPN solution for IIoT connectivity has no monthly fees if data use is under 5 GB a month. (Courtesy: AutomationDirect)
To accomplish this, the local VPN router makes a VPN connection to the cloud server immediately upon startup, but the VPN client only connects upon a verified request from the remote user. Once both connections have been made, all data passing through this VPN tunnel is secure.
Communication is initiated by the local router to the cloud-based server via an outbound connection through standard ports that are typically open, such as HTTPS. This usually requires no changes to the corporate IT firewall, thus satisfying IT security concerns. Traditional VPN solutions require IT involvement and oversight in order to open inbound firewall ports, which often poses problems.
Hosted VPN solutions only require simple router configuration because the router (Fig. 2) is connected to a predefined cloud server. This allows the hosted VPN vendor to deliver the router preconfigured, so the user only needs to add basic network information. The router’s default firewall settings keep the plant floor network separate from the corporate network.
2. By only providing the functionality needed for IIoT connectivity, this AutomationDirect StrideLinx VPN router, installed on the far right of the DIN rail and connected to the PLC, simplifies implementation and use. (Courtesy: AutomationDirect)
The VPN router should include Wi-Fi and 4G LTE connectivity options, in addition to a wired LAN option. The Wi-Fi option allows the router to operate in access point or client mode. With access point mode, wireless devices connected to the router are on the LAN network, allowing plant personnel to access the control system local area network (LAN) wirelessly, rather than opening the panel to access the physical LAN connection ports. With the 4G LTE option, access can be provided from remote locations without internet access, or from locations that will not provide access to their corporate network.
Security risk is minimal with this solution because the remote client connection to the cloud server uses the robust encryption standard SSL/TLS. The required TLS key exchange, crucial for security, is done in accordance with industry standard 2048-bit RSA with SHA-256.
To further enhance security, some vendors provide advanced user management, event logging, and two-factor authentication. This method of authentication requires a second time-based password generated at login, providing an extra level of security.
A typical hosted VPN solution has a free monthly bandwidth allocation for basic operation, and then offers a premium plan for additional bandwidth. Normal troubleshooting and programming needs normally fall under the free data allocation, but extensive data monitoring or video surveillance may require additional bandwidth.
Hosted VPN Requirements
With the recent rash of data breaches, it’s important to have a high level of trust in the selected hosted VPN vendor, as it will be responsible for securely storing data and making it available to only those who need it. This is of course a concern for any IIoT implementation, and some hosted VPN vendors have much better security measures in place than others.
Monthly costs incurred for exceeding the free data bandwidth usage must also be considered, particularly as those costs are zero for a traditional VPN solution. Again, these costs vary widely from one vendor to the next, and should be evaluated closely. IT support is not needed because the solution is simple to implement and maintain, with acceptable security built in.
With this solution there are some limits in terms of advanced routing features, although these features aren’t required in most applications. Complex IIoT implementations such as machine-to-machine networking, advanced Network Address Translation (NAT) configuration, and access control lists may require a traditional VPN implementation.
Specific features offered by the router vendor can enhance design flexibility and value, easing design considerations. Some of the leading features include IIoT data logging, widgets for configuring remote access dashboards, a web-based platform for router configuration, and a digital input for enabling/disabling remote access.
IIoT data logging provides collection, storage, and display of data via a cloud-based platform, allowing storage of and access to a virtually unlimited amount of data, while only requiring payment for the required capacity. This makes it feasible to start with a minimal amount of storage, and then increase if needed by paying more each month. The vendor’s cloud-based data logging usually requires an additional license or subscription to collect and store the data in the cloud platform.
A traditional VPN solution requires a third-party HMI, either PC-based or embedded (Fig. 3), to provide data logging and widgets for configuring remote access screens. Many hosted VPNs do not require an HMI because they provide their own graphical interface capabilities. With these solutions, users can configure dashboards using widgets for remote access via their PC or mobile device (Fig. 4). Users can also configure alerts and notifications to indicate when parameters fall outside a predefined range. Creating remote access viewing screens can be cumbersome if this feature is not provided, so this must be taken into account when evaluating competing hosted VPN solutions.
3. When traditional VPNs are used, a local HMI, such as this AutomationDirect C-more panel, is often part of the solution. (Courtesy: AutomationDirect)
4. This AutomationDirect StrideLinx secure remote access dashboard is easy to configure using provided widgets. (Courtesy: AutomationDirect)
Some hosted VPN solution vendors provide quick and easy configuration of the VPN router via a web-based platform. Ideally, this will only require account registration, configuration, and downloading of router settings, and installation of a secure client on a PC. A web-based platform is better than PC-based configuration because updates can be made without having to reinstall a new version of the configuration software on a PC—particularly important when new features are added on a regular basis.
For enhanced safety, the VPN router should have a discrete input to locally enable or disable communications via a manual switch to prevent remote control of a machine during maintenance periods.
Traditional VPN Solution
This solution uses a local VPN router to connect through the internet, with a secure VPN tunnel to a second remote VPN router or software client (Fig. 5). After these connections are made, remote users can access automation components connected to the local router through the VPN tunnel.
5. With this traditional VPN solution, two routers are commonly used, each requiring IT support both locally and remotely. (Courtesy: AutomationDirect)
There is no cloud server between the two devices with either method of connection: VPN router to VPN router, or VPN router to VPN software. This traditional VPN solution may be needed when large amounts of data must be continuously exchanged between the local and remote sites, as with remote viewing of local video.
This solution was the only method of secure two-way access prior to the fairly recent introduction of cloud-based remote access solutions via a hosted VPN around 2012, so it’s widely used. But it is complex, and can therefore be costly in terms of internal resources required for support, both at the local and the remote site.
Traditional VPN Requirements
The IT team must have the capability and willingness to support this solution at both the local and remote sites for each installation. If this solution is being implemented by an original equipment manufacturer (OEM) machine builder, for example, the OEM must consider every customer site, and make sure all of its customers can provide the required high level of IT support. In some cases, the OEM may have to customize its remote access solution for each customer, greatly adding to implementation and support costs.
Depending on the networking requirements, this solution may have approximately the same initial costs as a hosted VPN solution if a router and VPN client implementation is chosen. For applications such as machine-to-machine where two routers are required, the traditional VPN solution has a more expensive initial cost.
IT resources are required to configure the connection, adding to design and implementation costs. Larger companies may have a dedicated IT staff to provide this support, but most smaller companies will not, requiring outsourcing of required IT resources. Although ongoing external costs are lower because there are no monthly cloud service fees, internal costs are higher due to the need for IT support.
For many companies, a security concern is created because IT must open an inbound VPN port on the firewall. This is done to provide full remote control and monitoring by creating a single IIoT network joining local and remote users. This raises a security concern as the inbound VPN port must constantly be protected with a high level of access control. In addition, ongoing security vigilance is needed to ensure router and VPN protocols remain up to date. Other technical considerations must also be addressed, including:
- Configuring firewalls
- Addressing subnet conflicts across sites with similar network design
- Controlling user management and access
- Implementing event logging
- Creating and managing security certificates
- Applying advanced networking knowledge
- Configuring clients at each connection point
Even with these challenges, a tradition VPN is preferred if the required IT staff is available and the application requires high data bandwidth, or if there is a requirement to not rely on a vendor for a hosted VPN solution.
Using a Hosted VPN
In our first example, an OEM’s machine does not require remote video monitoring. Local operator interface is provided by an embedded HMI with limited data logging and storage functionality.
The OEM machine builder needs secure remote access and an easy-to-configure data dashboard for remote monitoring. VPN access is required to provide remote troubleshooting, debugging, and programming of the machine’s PLC and HMI. Both the OEM and its customer require monitoring of the machine’s most important operating parameters on mobile device dashboards.
The OEM machine builder doesn’t have an IT department—just one part-time person who set up its internal network. Its automation staff consists of one control systems professional who is an expert when it comes to programming PLCs and HMIs to automate their machines, but is not very familiar with IT, VPN, and router technology. Most of the OEM’s customers are not willing or able to reconfigure their firewall, eliminating the traditional VPN option.
In this case, a hosted VPN solution is the best choice because it will satisfy the OEM and customer requirements, and it can be implemented without the assistance of IT staff.
Data logging is provided in the cloud, so the local HMI’s limited data storage capability is not an issue. Widgets can be used by the machine builder to create dashboard screens for viewing on remote devices by many different users. When full remote control and monitoring is required via the IIoT, it can be provided by installing a lightweight software client on a PC, which can connect to the cloud from any location worldwide.
Using a Traditional VPN
In this second example, the OEM sells very large and complex printing presses with thousands of automation system I/O points, and its customers require the OEM to provide support of the machine, including uptime and throughput guarantees. The OEM needs to remotely monitor and support its presses worldwide to make sure guarantees to customers are met.
The OEM has considerable IT expertise and is capable of implementing a traditional VPN, and each of its customers is willing to allow the required firewall modifications.
Each press also has multiple video cameras installed for remote viewing, a necessity for solving some of the more complex troubleshooting issues. Each printing press has a full-featured PC-based HMI installed to provide local viewing and data storage, with high-speed remote access to the HMI and its stored data required at all times. Therefore, large amounts of operating data must be continuously transmitted to the remote corporate control center.
A traditional VPN is the right solution in this application because of the significant amount of data exchange required, which could be cost-prohibitive for a hosted VPN, and because the right IT resources are available to support the solution at the control center and at each site.
Decisions
When implementing an IIoT solution for remote access, a VPN is necessary to provide the required security. Older solutions without a VPN simply don’t provide the needed level of protection from intrusion.
Once the decision has been made to use a VPN for remote IIoT access, the two main types of solutions are a hosted VPN and a traditional VPN. The hosted VPN is the more modern solution and works well in most instances. The traditional VPN provides the utmost in performance for implementations requiring very high bandwidth, but is more complex to design, install, and support.
Jonathan Griffith is the product manager for Industrial Communications & Power Supplies at AutomationDirect. Prior to joining AutomationDirect in 2015, he worked at the Wi-Fi networking company ANADIGICS from 2002 to 2014. Griffith holds three degrees, all from the Georgia Institute of Technology: an MBA, an MSEE, and a BSEE. He can be reached via e-mail.