Fear the Hacker! Robot Security is a Growing Threat
In 2018, there could well be 1.3 million robots in factories around the world. According to a recent book What to Do When Machines Do Everything by Malcom Frank, Paul Roehrig and Ben Pring, 12% of jobs will be performed by automated systems over the next 10 to 15 years.
The rate at which companies are turning to robotic solutions is obviously high—and with that comes the potential for these systems to be hacked. Recent studies show that the potential for cyberattacks against robots is great, and that operators need to take the necessary precautions.
The Current State of Robot Security
A recent report, written in the spring of 2017, summarized the current state of industrial robotic security. Researchers in the Department of Electronic, Information, and Bioengineering at the Politecnico di Milano and the cybersecurity firm Trend Micro conducted the study. The researchers reached out to 50 different experts in the robotic field, which included researchers; engineers from companies like ABB, KUKA, and Comau; safety engineers; and the chair of the Industrial Robotics group at EU Robotics.
About 30% of the respondents found the default safety measures in their robotic machines too limiting and 60% chose to customize the parameters for specific use cases. The survey highlighted the issues inherent to robot development cycle programs, in that operators are not accountable for any changes that may occur to the robot programming.
Some 28% of the respondents did not enforce access control policies, and 76% had never performed a professional cybersecurity assessment test on their infrastructure. The most alarming number: 30% of the robots were accessible from the internet, and 50% of respondents did not believe that cyberattacks were a realistic threat.
The researchers had three key takeaways:
- The increased connectivity of robotic systems to corporate networks, likely due to the increase of Internet of Things (IoT) systems and connected sensors, are exposing robots to potential cyberattacks.
- The increased use of collaborative robots (cobots) has made safety a No. 1 concern. The fact that these cobots are also connected to internet networks means that the potential attacks from disruptors may interrupt safety protocols that control cobots. Safety mechanisms in software are increasing as a direct result.
- The awareness of security risk is scarce, with many operators not taking the appropriate actions to protect their robots from cyberthreats.
The Who, What, and Why of Attackers
The list of attacker goals breaks down into four different categories. The first is the “production outcome-altering” attack. In this scenario, the attacker wants to inject faults or defects in the production process. These defects can inflict loss of production and revenue on the line. This can also saddle the parts provider with a bad reputation, creating an advantage for competition.
The next attack is the “physical damage” approach. This could be an attack on the physical equipment itself or on the operator. It can be accomplished by manipulating safety protocols, making the operators and machine vulnerable to destructive movements.
The third category is the “production plant halting” attack. This is a severe attack where the time to repair is so great that production comes to a complete halt.
The last scenario is an “unauthorized access” attack, where the attacker is attempting to steal sensitive data from the machines or company through remote access.
In all cases, the attacker of a robotic system is most likely an insider. This means an individual who is familiar with the systems of robots and their programming. The attacker is technically minded and has the skill set necessary to reprogram and manipulate these robotic systems. Access to the software of the robots depends on the system. Some robot manufacturers make there firmware available online for updates. Some have online-simulated environments for programmers to practice their subroutines. Unfortunately, this also provides attackers with a digital space to practice their attacks in. Access to recent firmware can come from the resell of old robotic components, as the sale of robot CPUs is not restricted.
The type of attacker breaks down into three groups:
Network attacker. This type of attacker uses the hardwired LAN connection to the robot via either the factory network or remote service facilities. This form of attack can be executed from a computer terminal or by using access points on the robot (e.g., USB) to hack the robot.
Remote attacker. This attacker uses the internet to attack robots. More robots are becoming internet capable, and thus becoming connected to company’s internet network as a way of supporting off site access. However, this makes these robots vulnerable to attack. The researchers of the study performed a search for robotic controllers and were able to find three distinct ABB controllers. These attacks can happen over the internet; a virtual private network connection; or a general packet radio service network that allows 2G, 3G, and WCDMA mobile networks to transmit IP packets to external networks like the internet.
Physical attacker. The physical attack is the simplest and most common type, using the robot’s handheld interface.
The video below is the successful hack of a robotic arm conducted by Politecnico di Milano and Trend Micro. ABB has since patched the vulnerabilities found in this attack.
How to Protect Your Robots
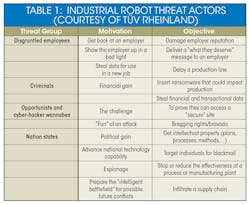
Another recent study from TÜV Rheinland (http://www.openskycorp.com/resource-center/blog/industrial-robotics-cyber-security/) highlights not just the potential attacks against robots from cyber attackers, but the standards and a checklist of actions users can utilize to protect their robotic equipment. Industrial robot manufacturers and operators need to review all cybersecurity risks. Once the risks have been determined, they can implement the following standards to help them prevent attacks.
The following are checklists from TÜV Rheinland that can be performed by manufacturers, integrators, and operators alike to help secure better robot security.
Manufacturers should undertake a:
- Review of robot security design
- Hazard analysis and threat modelling
- Creation of a Traceability Risk Matrix
- Secure code review
- Penetration and dynamic test to identify vulnerabilities
- Review of components for potential cyber security weaknesses
- Review of appropriate key security controls
- Security incident response plan review
- Legal and regulatory assessment
- Software update and patch process review
- Review of vulnerable design intersections within the device architecture
Integrators should undertake a:
- Review of vulnerable design intersections within the system architecture
- Review of the device source code across the system
- Development of a Traceability Risk Matrix
- Secure code review of other associated systems
- Penetration and dynamic test to identify software vulnerabilities
- Review of other components for potential cyber security weaknesses.
- Review of and suggest appropriate security controls
Operators should:
- Develop a security incident response plan
- Review software update and patch management processes
- Undertake a cyber security risk review of the plant facility and review vulnerable design intersections